
Secure Updates & Device Management
for Embedded & IoT Devices
We develop customized update strategies for your fleet management. CRA-ready.
Request a consultation today.Why a well-planned update strategy is essential for IoT devices.
Fleet Management
Regular software updates for IoT devices are essential to ensure security, functionality, and efficiency.
Without a consistent update strategy, companies risk security vulnerabilities, downtime, and rising maintenance costs. What matters is not only software development itself, but also managing and rolling out updates effectively.
Beyond product quality, the EU’s Cyber Resilience Act (CRA) also plays a decisive role: starting in December 2027, IoT devices must provide secure update capabilities. Learn more about the Cyber Resilience Act.
As your development partner, we take care of the entire fleet management execution process – from strategy to secure rollout. This minimizes downtime and maximizes efficiency!
We understand the challenges of update management for embedded devices.
Updating and managing large device fleets is becoming increasingly complex. Current solutions lack scalability, create vendor lock-in, and fail to meet the requirements of security and AI. As a result, companies face long update cycles, high costs, and insufficient guarantees of software integrity.
We have solved exactly these problems:

Complex & inefficient update management
across diverse OT & IoT fleets

Heavy toolchains
and high device resource consumption

Weak robustness,
missing failsafe mechanisms

No security-by-design approach

Lack of standards,
vendor lock-in and limited interoperability

Slow updates
with high bandwidth demand

No proof that installed software
or SBOM is executed at runtime

AI workloads amplify update load
and traceability needs
We understand the challenges of update management for embedded devices.
Updating and managing large device fleets is becoming increasingly complex. Current solutions lack scalability, create vendor lock-in, and fail to meet the requirements of security and AI. As a result, companies face long update cycles, high costs, and insufficient guarantees of software integrity.
We have solved exactly these problems:

Complex & inefficient update management across diverse OT & IoT fleets

Heavy toolchains
and high device resource consumption

Weak robustness,
missing failsafe mechanisms

No security-by-design approach

Lack of standards,
vendor lock-in and limited interoperability

Slow updates
with high bandwidth demand

No proof that installed software
or SBOM is executed at runtime

AI workloads amplify update load
and traceability needs
From Challenge to Solution.
This is how we make your update and fleet management ready to meet the demands of today and tomorrow.
Structured and secure updates
- Ensuring consistent and error-free updates through structured and automated processes
- Mechanisms to prevent inconsistent software versions
- Efficient rollback strategies to guarantee 24/7 operations
Efficient Management of Software Updates
- Management of feature-based updates with modern tools such as Git
- Support for differential (delta) updates to reduce data volumes
- Use of state-of-the-art security standards in communication
Automation & Quality Assurance through CI/CD
- Use of automated build pipelines for quality assurance
- Integration of automated tests along the testing pyramid
- Implementation of well-designed software and hardware tests
Scalable Deployment and Fleet Management
- Management of large device fleets with scalable tools
- Efficient OTA updates of OS (kernel, drivers, libraries) and applications
- Mechanisms to minimize downtime and operational disruptions
Security by Design
Many device management solutions focus exclusively on updates and deployment. Our fleet management platform goes far beyond that.
Security is integrated into the very foundation of the architecture and supports the entire lifecycle of a device.
Our fleet management platform combines:
- secure update processes
- continuous vulnerability monitoring
- transparent software versions
- automated security and compliance reports
This creates traceable security processes for device fleets, which is a key requirement for audits and regulatory compliance, such as the Cyber Resilience Act.
Your Benefits at a Glance.
Technological excellence – from security-by-design to AI readiness.

Safe updates with signed, attested binaries,
verified before install

Verifiable SBOM at runtime
with rollback and health checks

Self-healing devices
through A/B partitioning

Security by Design
in focus right from the start

Hardware and vendor independence
- Linux, RTOS, ARM, x86, custom PCBs
- Daisy-chain updates for child devices

Low-bandwidth updates
(OTA and delta)

Secure remote access
to any device

Robust and failsafe
update process

AI-ready with hardware acceleration
for ML/AI deployment

Global compliance with EU Cyber Resilience Act,
NIST (US), NCA (Middle East)

Safe updates with signed, attested binaries,
verified before install

Verifiable SBOM at runtime
with rollback and health checks

Self-healing devices
through A/B partitioning

Security by Design
in focus right from the start

Hardware and vendor independence
- Linux, RTOS, ARM, x86, custom PCBs
- Daisy-chain updates for child devices

Low-bandwidth updates
(OTA and delta)

Secure remote access
to any device

Robust and failsafe
update process

AI-ready with hardware acceleration
for ML/AI deployment

Global compliance with EU Cyber Resilience Act,
NIST (US), NCA (Middle East)
Fleet Management - Reference Architecture
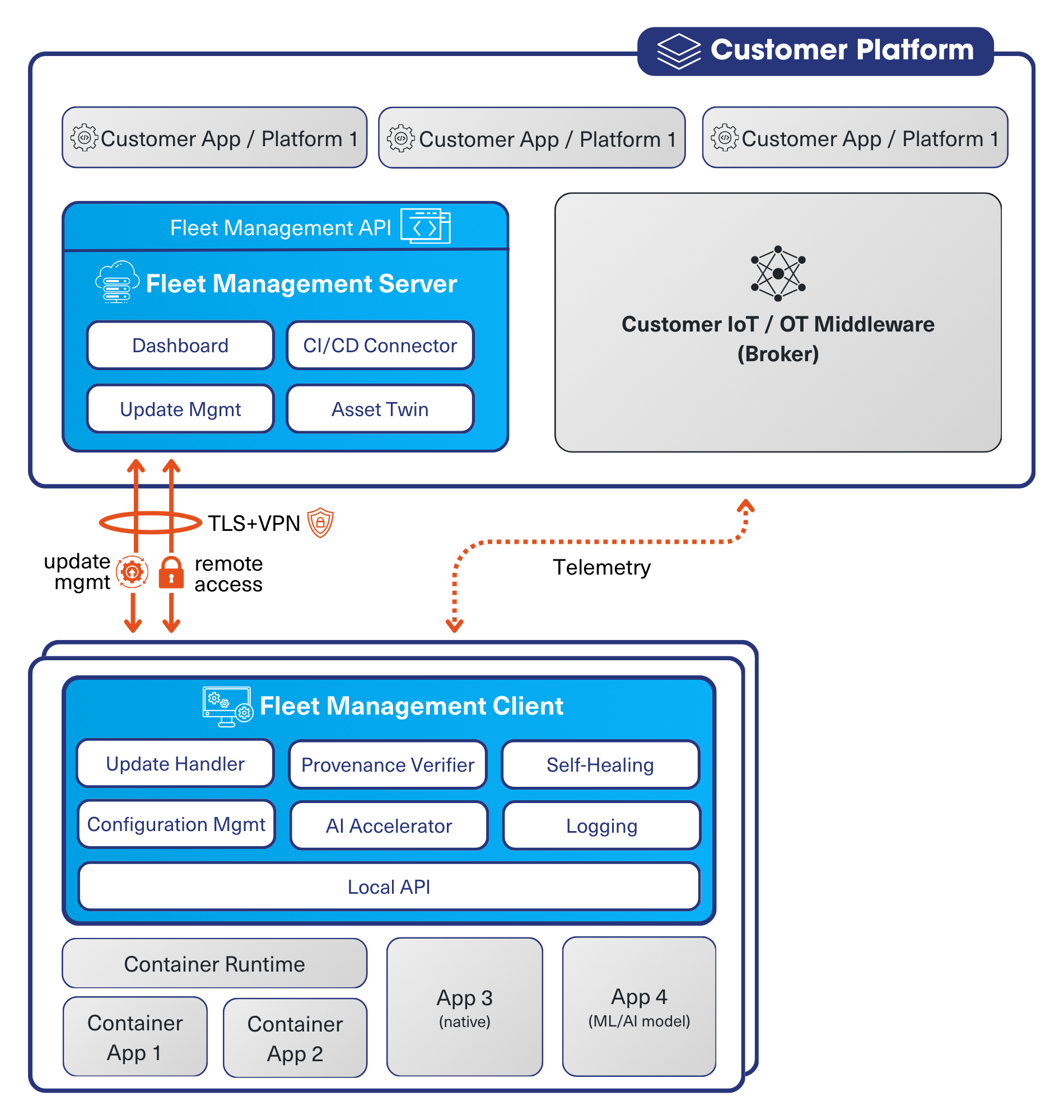
Compliant with global standards – without compromise!
Legal requirements for software security and traceability are increasing worldwide. With our solution, you can ensure that your device fleet always complies with the latest regulations – from the EU Cyber Resilience Act (CRA) to NIST standards (USA) and NCA guidelines (Middle East).
Cyber Resiliance Act
Binding security standards for Europe
National Institute of
Standards and Technology
Standards for information security and software integrity
in the US
National Cybersecurity Authority
Regulations and standards for information security
and critical infrastructures in the Middle East
How we support you in Fleet Management.
Our Services.
How we support you in Fleet Management.
Our Services.
Software Development Processes
and Workflows
- Consulting and optimization of software and deployment development processes
- Automation of software builds and tests
- Standardized security concepts for embedded software
Embedded Linux Distributions und Configurations
- Development of optimized embedded Linux distributions
- Implementation and maintenance of efficient Yocto Linux configurations & images
- Support for customer-specific hardware
Efficient Fleet Management and Updates
- Managing and monitoring large device fleets
- Scalable fleet management for application and OS updates
- Efficient delta updates to minimize bandwidth usage
Flexible pricing model
Our solution adapts to your needs:
-
One-time device license with self-hosting – setup support available on request
-
Or a subscription/license model with hosting by Danube Dynamics in a secure Austrian cloud

Nico Teringl, MSc
CEO, Danube Dynamics
"Our mission is to equip technology leaders and engineering teams with the right tools and workflows to efficiently manage complex device fleets. Let’s talk about your challenges."
Technological Excellence with Danube Dynamics.
With our secure, scalable, and future-proof solution, we guarantee that managing your device fleet will no longer be something you need to worry about. Instead, our solution will make you ready for all current and future requirements, such as standards and certifications, artificial intelligence, and cybersecurity.
Preventing downtime
with structured update processes
Reduced maintenance costs
with optimized workflows
Minimizing security risks
with state-of-the-art tools
How we support our customers.
Companies in industrial automation, medical technology and telecommunications trust Danube Dynamics:
60%
Medical technology company: Update duration reduced by 60%
50,000
Telecommunications:
Central management of 50,000 devices.
80%
Industry: 80% lower data volume per update with delta updates
Fleet Management - FAQ:
Embedded and Internet of Things (IoT) devices are software-driven products that are becoming increasingly intelligent and interconnected.
Throughout their entire lifecycle, they must be maintained, secured, and able to receive updates. The Cyber Resilience Act (CRA) will make these requirements mandatory and verifiable for the first time.
Devices that cannot be operated, maintained and updated securely will be unmarketable in the long term. Furthermore, the CRA provides for heavy fines and regulatory measures in the event of violations.
At the very least, this is necessary when devices in the field need to be maintained, updated or managed by multiple roles.
Even small fleets can lead to significant manual effort and an increased risk of error without a structured update and access strategy.
However, it is important to note that fleet management should be considered from the outset of the development phase. While it is not absolutely necessary to integrate a complete platform from the outset, a clear update strategy and operational architecture must be planned for early on. What is crucial, however, is that a clear update strategy and operational architecture are planned from the outset.
Introducing a complete fleet management system after many devices have already been shipped is usually significantly more time-consuming and technically more challenging.
Yes.
Our architecture addresses key CRA requirements, such as:
- controlled update capability throughout the entire lifecycle
- traceability of software versions
- SBOM-based vulnerability assessment
- documented and auditable processes.
Fleet Management is the technical prerequisite for putting these requirements into practice.
The solution can be operated entirely on-premise and also supports air-gapped networks. There is no requirement to use the cloud.
The server side of the platform can be hosted by the customer and runs on any Linux-based system.
Hosting by Danube Dynamics is also available as an option.
Updates are cryptographically signed and validated before installation.
The platform uses A/B partitioning:
- Updates are first installed on an inactive system partition
- After a successful boot, the new version is activated
- If an update fails, the system automatically reverts to the last working version. The incident can be tracked centrally. The system remains bootable.
Communication is encrypted and certificate-based. Devices uniquely authenticate themselves to the infrastructure. Unauthorized devices or tampered updates are technically prevented.
Yes.
SBOMs are generated for operating systems and applications. These are regularly checked for known vulnerabilities. Affected devices can be clearly identified and updated as a priority.
Yes.
The architecture is modular and horizontally scalable. It can scale from pilot projects to large device fleets without requiring any fundamental architectural changes.
There are generally two operating models:
Managed Service:
- Platform hosting, which is provided by Danube Dynamics.
- We handle operations, updates and infrastructure.
- This is billed via a monthly fee per device.
Unmanaged Service:
- Hosting and operation are handled by the customer.
- Annual platform licence including updates.
- The customer operates the infrastructure.
Additionally, Service Level Agreements (SLAs) can be arranged to define the scope of support and response times.
Let’s develop your update strategy together.
We believe that managing embedded and IoT devices is an opportunity – for process optimization, increased security, and innovation.
Contact us to learn how we can take your device fleet to the next level.